Security & Encryption
epub |eng | 2020-05-06 | Author:Mujthaba Hassan
6.2 Simple HTTP DoS Attack To carry this out, you need to install Fiddler first, and then visit to a website. You could then select the request and press Shift ...
( Category:
Privacy & Online Safety
January 9,2023 )
epub |eng | 2022-12-12 | Author:Garg, Rishabh; [Garg, Rishabh]
8.7.5.3âChinese Military Beijing, China â Defense and Armed Forces: The Chinese military and government are gearing up to use blockchain cybersecurity to protect critical government, military, and other intelligence data. ...
( Category:
Encryption
January 5,2023 )
pdf |en | | Author: Reza Montasari
( Category:
Networking
January 5,2023 )
epub |eng | | Author:Renee Dudley
* * * By 2012, FBI leadership recognized that most crimes involved some technical elementâthe use of email or cell phones, for example. So that year, it began to prioritize ...
( Category:
Viruses
January 1,2023 )
pdf | | 2022-11-16 | Author:Stiennon, Richard;Ernst, Russ B.;Forslund, Fredrik;
( Category:
Online Safety & Piracy
December 23,2022 )
pdf | | 2020-08-07 | Author:Catarina Charneira, João Nunes, and Alexandra M. M. Antunes
( Category:
Encryption
December 22,2022 )
pdf | | 2022-12-15 | Author:Martin Sims
( Category:
Networking
December 21,2022 )
pdf | | | Author:Unknown
( Category:
Privacy & Online Safety
December 19,2022 )
pdf | | 2022-11-28 | Author:Rocchi, Walter;
( Category:
Privacy & Online Safety
December 11,2022 )
pdf |en | | Author: VX Underground
( Category:
Viruses
November 30,2022 )
pdf | | 0101-01-01 | Author:Derek Fisher
( Category:
Viruses
November 28,2022 )
pdf | | 2022-04-11 | Author:Simon Bisson, Mary Branscombe, Chris Holder, and Anand Raman
( Category:
Viruses
October 14,2022 )
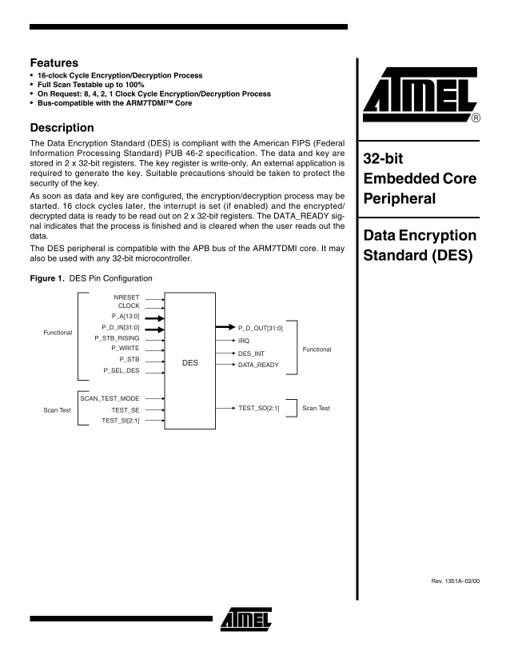
pdf | | | Author:Atmel Corporation
( Category:
Cryptography
October 13,2022 )
pdf |en | | Author: Bradley Fowler, Kennedy Maranga
( Category:
Encryption
October 11,2022 )
pdf | | 2015-08-26 | Author:Courtney Bowman, Ari Gesher, John K. Grant & Daniel Slate
( Category:
Privacy & Online Safety
October 5,2022 )
Categories
| Cryptography | Encryption |
| Hacking | Network Security |
| Privacy & Online Safety | Security Certifications |
| Viruses |
Popular ebooks
Mastering Azure Security by Mustafa Toroman and Tom Janetscheck(3051)Future Crimes by Marc Goodman(3026)
Mastering Python for Networking and Security by José Manuel Ortega(3004)
Blockchain Basics by Daniel Drescher(2928)
Practical Threat Detection Engineering by Megan Roddie & Jason Deyalsingh & Gary J. Katz(2856)
Effective Threat Investigation for SOC Analysts by Yahia Mostafa;(2687)
Mastering Bitcoin: Programming the Open Blockchain by Andreas M. Antonopoulos(2540)
From CIA to APT: An Introduction to Cyber Security by Edward G. Amoroso & Matthew E. Amoroso(2511)
Machine Learning Security Principles by John Paul Mueller(2420)
Practical Memory Forensics by Svetlana Ostrovskaya & Oleg Skulkin(2406)
The Art Of Deception by Kevin Mitnick(2326)
The Code Book by Simon Singh(2250)
Attacking and Exploiting Modern Web Applications by Simone Onofri & Donato Onofri(2092)
Operationalizing Threat Intelligence by Kyle Wilhoit & Joseph Opacki(2082)
Solidity Programming Essentials by Ritesh Modi(2015)
Hands-On AWS Penetration Testing with Kali Linux by Benjamin Caudill & Karl Gilbert(1920)
Wireless Hacking 101 by Karina Astudillo(1873)
DarkMarket by Misha Glenny(1865)
Applied Network Security by Arthur Salmon & Michael McLafferty & Warun Levesque(1855)
Mobile Forensics Cookbook by Igor Mikhaylov(1828)